
The author of the article is Jameson Lopp, technical director of the Bitcoin startup Casa and one of the Bitcoin developersCore. Originally published on the Casa blog.
When we talk about the security of crypto wallets,The focus is on ensuring that private keys do not fall into the wrong hands. It is believed that if an attacker gains access to private keys, the game is over.
However, wallet security is notonly to restrict access to private keys. We must also monitor the receipt and withdrawal of funds from the wallet, as these operations can be intercepted by an attacker in order to redirect BTC to his address.
Although no wallet software can protect you from all possible problems, we at Casa we have come to the conclusion that browser wallets are the most vulnerable for a number of reasons.
Phishing and malware
Phishing is the practice of deceiving a user through a redirect to a site that simulates a real one, in order to obtain user credentials or download a modified version of a wallet.
For example, by logging into the conditional site C0inbase,an attacker can obtain a username, password, and even 2FA to access a Coinbase account. For years, fraudsters have been manipulating search engine advertising to trick users into a malicious website.
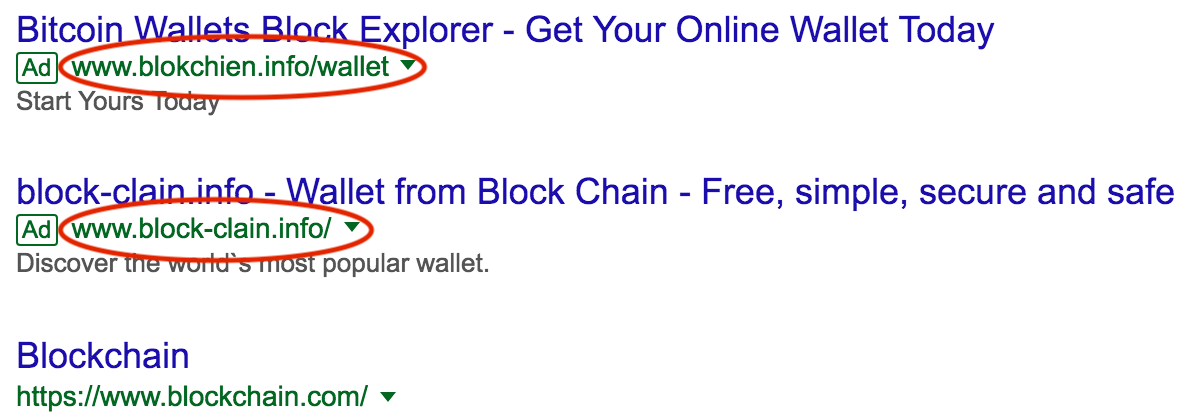
Although phishing attacks on web wallets arecommon practice, they also occurred in relation to desktop wallets that connect to remote servers. Thus, users of the popular Bitcoin wallet Electrum were attacked by a false update notification with a malicious version of the wallet.
Even users of the Trezor hardware wallet,whose private keys are stored securely on a separate device, were vulnerable through the Trezor web wallet - attentive users might notice that the SSL certificate does not match the domain. Trezor impostor sites often pop up too - users who accidentally type in the wrong URL can be redirected to a malicious site that looks exactly like the Trezor web wallet.
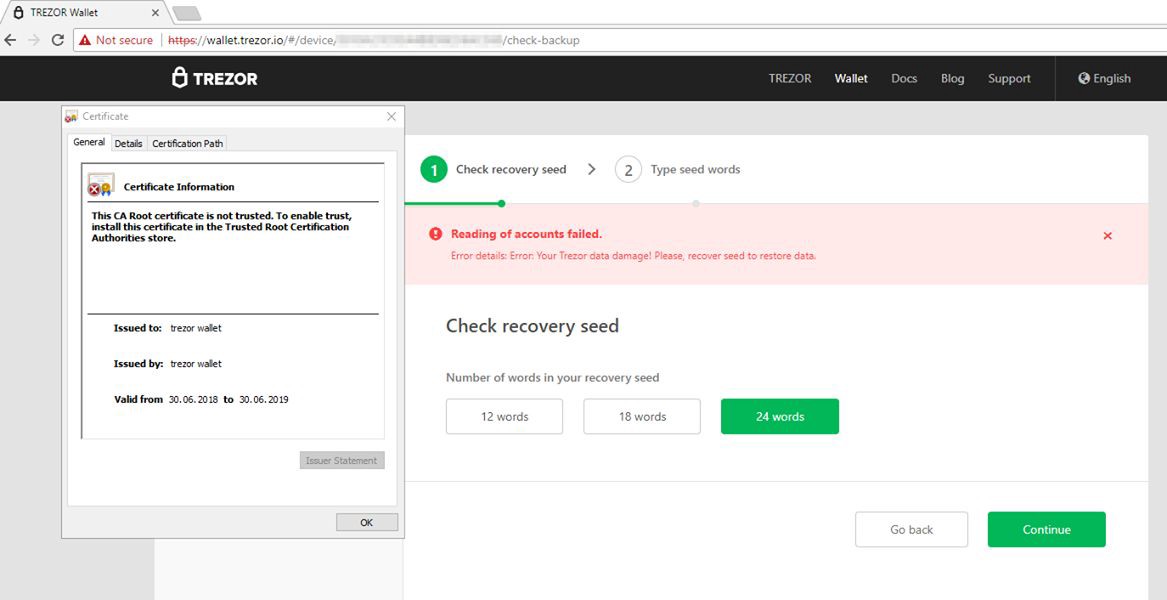
Attackers are well aware that they cannotRemotely extract private keys from individual hardware devices, so they exploit weaknesses in the software that is used to interact with the device. Today, these attacks are quite simple and ask the user to enter a seed phrase, which in itself should raise suspicions, but many users still come across this.
Desktop Wallets SoftwareIt is also vulnerable to malware that could threaten I / O. This is due to the fact that desktop operating systems have many attack vectors, since they are used for a variety of tasks.
We know that attackers even gotcontrol over popular JavaScript libraries, which are known to be used in many bitcoin wallet software. This is a particularly difficult problem for many browser wallets, as many of them are developed in JavaScript.
There is a reason gold standardBitcoin wallet security is considered the use of a special hardware device such as Ledger / Trezor / Coldcard / etc. Such a device protects private keys from intruders and launches software that is highly resistant to cracking and ensures the integrity of the generated addresses displayed on the device’s screen.
Any software running ona general-purpose machine will be more easily attacked, although mobile operating systems are generally more resistant to hacking and block applications better through the sandbox.
Browser extensions
While desktop or mobile wallets can be used while ensuring the proper level of security for the operating system, any web wallets have very little protection.
And the providers of these wallets can do wrongmany, because security issues are not limited to the vulnerability of their own infrastructure, and in many cases are end-user problems. To protect against malware, the browser wallet should be used only on a separate computer, but most users will neglect this, putting themselves at risk of hacking.
One particularly troubling problem with browserswallets is that browser extensions can easily take full control of all data accessed through the browser. At the end of 2018, Kaspersky Lab experts discovered a Trojan that was specifically designed for browser wallets and installed malicious extensions.
The findAndReplaceWalletAddresses function performssearch for wallets for bitcoin and ether and replace them with the addresses of the purses of the attacker. In particular, this function works on almost all pages except those located in Google and Yandex domains, as well as on popular domains such as instagram.com. and ok.ru. Images of QR codes with wallet addresses are also replaced.
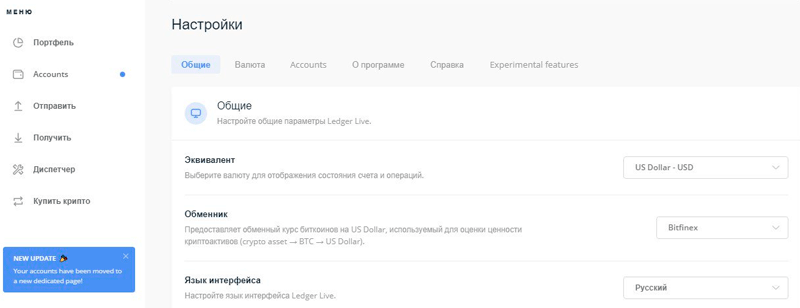
We suspect security concernsbrowsers are one of the reasons Ledger stopped supporting its Chrome extensions and instead requires users to install its desktop Ledger Live application.
Open source softwarecode, as a rule, provides greater reliability, but in mobile applications there are difficulties. We do not currently know how to prove that software installed through the iOS App Store or Google Play is the same software that is available in the open source repository.
Billing protocol which includesa cryptographically authenticated recipient address, the recipient address can also improve the integrity of payments, eliminating the attack of the "intermediary". The Bitcoin Improvement Proposal (BIP) 75 does this - it was proposed back in 2016, but it was not widely distributed due to possible problems with user privacy. Today, when sending large bictoin transactions, it is recommended to confirm the address through other channels (via video / audio) to make sure it is correct.
Do not trust your browser!
</p> 5
/
5
(
1
vote
)



