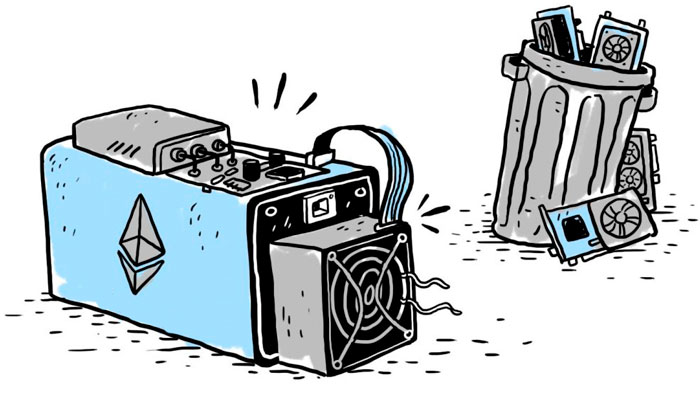
ProgPoW update aimed at limiting Ethereum mining using specialized ASIC miners,continues to cause lively discussions since unilateral encouragement by developers in February.
Now they have been supplemented by observations from a Kik user who discovered and described an interesting vulnerability. Instead of fighting ASIC miners, ProgPoW can make Ethereum mining much easier for them.
According to Kik, instead of the 256-bit sid used in the current Ethash mining algorithm, ProgPoW uses a 64-bit value, and compensates for the missing bits in “other ways”.
Looks like the current implementation of ProgPoW may not be so ASIC resistant after all.
Basically, ProgPoW hashing function uses a 64 bits seed, which ASIC can brute force «easily» instead of mining as they are expected to.
This needs more eyes on it to properly confirm. https://t.co/OqSp8tG2Ir
- Philippe Castonguay (@PhABCD) March 4, 2020
“Kik discovered that you can just run a memory-demanding function for one sid only once, and then find the headers and nonce values by increasing the extraNonce value”, Says mining expert Christie Lee Minehan.
Minehan generally confirms Kik's observations, butstates that the vulnerability remains to be proven in practice. To exploit the vulnerability, miners must meet some difficult conditions, but this is possible. If one of them can find the right approach, it will significantly increase the profitability of production for themselves and the difficulty for everyone else.
The solution to the problem is simple enoughprocessing algorithm. At the same time, the opponents of the update hope that the vulnerability of ProgPoW will force developers to once again think about the feasibility of activating it, or at least attract additional resources to its audit.
“It seems that the current implementation of ProgPoW may benot too protected from ASICs. ASIC can easily find the right value for this hash function instead of mining. ”- writes researcher Philippe Castongui.
5
/
5
(
1
voice
)





